Internet Safety Rules Every Widow Must Know

Short and Sweet Summary: If you’re not following mandatory rules to keep your personal data safe online, you’re ripe for hackers to infiltrate your accounts. But it doesn’t have to be that way. By adhering to these internet safety rules every widow must know, you can stop hackers in their tracks.
Our entire lives are digital nowadays.
Smart phones are filled with apps that let us accomplish most tasks, from bank transactions to shopping, almost exclusively online. It seems like we do everything with the push of a button or click of a mouse. Even if you’re not a savvy app user, you most likely conduct the bulk of your business online through your computer.
Because our internet habits make us more vulnerable to hackers, it’s easy for someone to intercept your personal information. Data like credit card and bank information can end up in the wrong hands if you’re not vigilant about securing your online presence.
Are you vulnerable to an identity attack? Can a hacker access your personal account information?
Probably.
Unless you’re following these ways to stay safe online.
You don’t need a PhD in computer coding to know how to protect your online privacy. There very simple and effective ways to keep your data safe.
Like these options below.
CHOOSE AN IDENTITY THEFT PROTECTION SERVICE
I’m a big proponent of limiting my online vulnerability. The easiest way I know how to do that is with an identity theft protection service.
I’ve had an Identity Guard account for several years to help me monitor and protect my personal information online. It brings tremendous peace of mind knowing Identity Guard continually monitors my social security number, credit card activity, bank accounts and other personal data to expose any unusual online activity.
I’ve written before about the benefits of an identity theft protection service, so I won’t go into that again here. You can check out these in-depth posts for more information:
- Why You Need an Identity Theft Protection Service
- How to Protect Your Identity – Expert Tips for Widows
CREATE STRONG PASSWORDS
One of the simplest internet safety rules to protect your online privacy is to create strong passwords.
What is a “strong” password? A strong password is long (at least 12 characters) with a combination of letters, numbers and special characters (like #, @ or *). Hackers have a harder time cracking the code on longer, more complicated, passwords.
But how do you create strong passwords that are long and complicated enough to withstand infiltration?
- Create Your Own Passphrase. You can make up your own password using methods like creating a passphrase you’re likely to remember. Something like, “I lived at 438 Turnberry Drive at age 10” could turn into the strong password Il@438TDat10.
- Use a password generator. Simply choose the password length (the longer the better) and whether to include symbols or other special characters. The password generator does all the work. You just copy and past the generated password into your account.
- Create random passwords. You can create your own random passwords by simply typing a combination of letters (both uppercase and lowercase), numbers, symbols or special characters. Like FGR76:Y34d&*? It doesn’t have to mean anything. It’s just a random set of characters at least 12 characters long.
It’s damn near impossible to remember all of your passwords, so you can keep track of your passwords in your own document (like I do in an MS Word table, but make sure to back up your data in IDrive…see below) or you could use a password manager to help you.
Either way, you need to save and keep track of your passwords in the best way for you.
If you decide to use an online monitoring service like Identify Guard (listed above) it also comes with its own password manager.
USE TWO-FACTOR AUTHENTICATION
Even though creating strong passwords is a simple way to protect your online privacy, you can take it up a notch with two-factor authentication.
Two-factor authentication (2FA), or sometimes called multi-factor authentication, is a method of securing additional information before allowing access to an account. Types of 2FA include fingerprint or facial scan, PIN, an authenticator code or text/email verification codes.
So basically, step 1 is you enter your password. Step 2 asks that you enter the 2FA request. If a hacker did manage to crack your password, chances are slim he or she would have access to the 2FA request information also.
For example, I have 2FA on my PayPal account. Anytime I sign into my account, I also receive a text code that I have to enter before PayPal will let me sign in. Some other accounts use the Google Authenticator app for 2FA. This app lets you keep track of multiple 2FA codes from various accounts. Click for Google Authenticator Android or iOS app instructions to learn how to set up and use this service.
You can verify if your online accounts have 2FA by logging into your account and searching for login or security settings. If a 2FA option exits, I highly recommend using it. Almost all social media apps like Facebook, Instagram and Twitter utilize 2FA. If you haven’t secured your online social media accounts, you can start there to see how the authenticator works.
Even though it can seem like a pain to take another step to access your account, it’s infinitely less painful that dealing with a security breach. That’s a big ass headache you don’t want to deal with.
CHECK EMAIL SENDER’S ADDRESS
I can’t tell you how many times I’ve received phishing emails that desperately want me to cough up my personal data. These emails look totally legit and appear to be from reputable companies, but they’re not.
It can be hard to tell what’s legit and what’s fake, though. These phishers are getting SO good at deceiving end users. But I have a really easy way for you to determine an email’s validity: look at the sender’s email address.
I get a lot of phishing emails from some entity pretending to be Go Daddy, the domain registrar and web hosting company. Some of the emails look pretty legit, like this one (I’ve blacked out my account info):
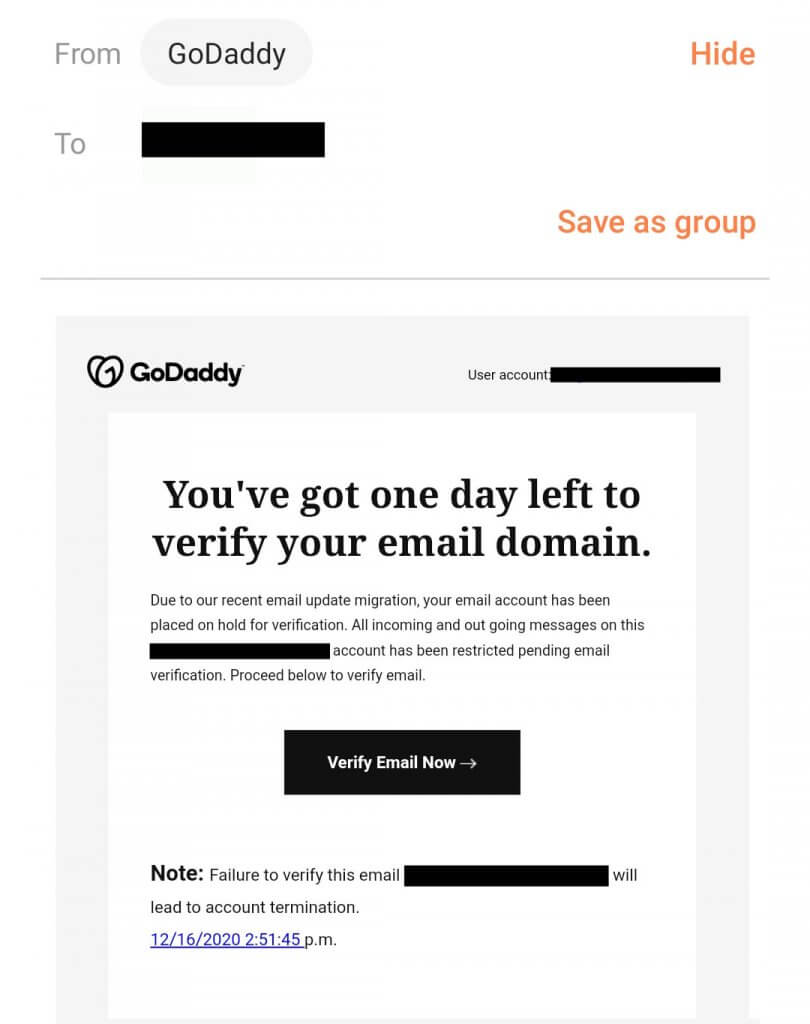
I mean, it’s not full of grammatical or punctuation errors (a big red flag) and it has the Go Daddy logo and all. But I never trust any of these kinds of emails. I’ve personally seen to many scams.
But, just to confirm my suspicions that it’s a fake email, I click on Go Daddy in the From: field to verify the email address. And the email address shows up as this:

Hmmnnn…doesn’t look like a Go Daddy email address to me.
Foiled again!
DELETE.
Anytime you get an email asking you to click a button or a link or to provide information, put on your common sense cap and ask yourself, “who is this really coming from and why is it so urgent?” Because chances are, legitimate companies aren’t sending you emails at the 11th hour asking for you to complete a step right now or your account will be suspended.
But what if the email address also looks legit?
I still wouldn’t click the link. I would do directly to my account and sign in there. If something needs to be completed in your account, the message will most likely be in your account settings.
BE VERY WARY OF EMAIL ATTACHMENTS AND LINKS
My rule of thumb is that I rarely click on an email attachment or link. It’s just not worth the risk. If you click a link from a hacker, he or she can infect your device with malware and steal your data in a matter of minutes.
And that’s another big ass headache to fix.
Of course if I’m talking to a family member and say, “hey send me a copy of your itinerary” because they’re visiting soon, I would open that email attachment because I’m expecting it. I mean, there are exceptions to every rule.
However, if I get an email with an attachment or link I wasn’t expecting, I won’t open it. As I said above, even if I can confirm the email looks like it’s from a reputable sender, I still won’t click any included links.
Whatever the email is asking you to confirm by “clicking the link,” you can confirm by signing into your actual account. Or calling the company to confirm what’s been sent.
NEVER USE FREE WI-FI TO SIGN IN TO YOUR ACCOUNTS
Free Wi-Fi has its advantages like surfing the net while you’re drinking your Grande iced skinny decaf hazelnut macchiato in the corner booth, but the major disadvantage is ZERO security.
Don’t sign into any of your accounts on public Wi-Fi because it will be open season on your data for every hacker from here to Timbuktu.
If you must check accounts or sign into secure data points while away from your secured home network, use your phone’s mobile hotspot or invest in a VPN.
CLEAR THE CACHE ON YOUR BROWSER
Every website you visit is recorded in your browser’s cache on both your computer and your phone. The reason a browser stores cached pages is to make it easier to “serve” that page up to you when you revisit the site. The load time is much faster when your browser doesn’t have to keep requesting new pages.
As good as this sounds for speed, it’s bad for your personal data. When you visit sites and your online activities are stored in the cached pages for days or even weeks, a hacker has ample opportunity to view your cache and steal your data. Sometimes the cached pages contain your personal data from pages you’ve signed into on your accounts.
All the hacker needs to do is mimic the pages you’ve visited (and they can get this from the sites you visit) and serve you up a page that asks for your personal sign-in information. And you’re none the wiser.
You also don’t want to give the websites you visit the ability to track you and follow your online habits. Because then unscrupulous people target you for scams because they know what you’re likely to click on or purchase.
To learn how to automatically clear the cache on your specific browser, click here.
BACKUP YOUR FILES
Your computer and phone contain lots of files that would be hard to replace if hacked. Do yourself a favor and routinely backup your files.
A set-it-and-forget-it option for data backup is IDrive. This daily cloud backup option automatically saves your data from your computer and/or your phone for easy retrieval. After your initial backup is complete, you can set your own backup schedule to fit your needs.
If anything happens to your computer, whether through a malicious hack or just a random accident, your files are intact.
You can also save your data to an external hard drive if you want more control over your backup options. And you can backup or restore data on your Android device or iPhone following a few simple instructions.
Whichever way you decide to go, just decide to make a back up plan and stick to it.
WIDOW WRAP UP
There are many more internet safety rules you can research to protect your online privacy. You could Google “internet safety” or “how to protect my data online” and learn other ways to protect yourself.
So, while this isn’t an exhaustive list, it’s a good place to start. Just doing the few things listed here puts you leaps and bounds above many internet users who don’t have a clue how someone hacked their computer or hijacked their personal information.
It’s imperative that you are aware of how to keep your personal information safe online.
And it’s not rocket science once you know what to look for.